Arthur Besse
cultural reviewer and dabbler in stylistic premonitions
- 12 Posts
- 38 Comments

 10·13 days ago
10·13 days agoAll two-letter TLDs are ccTLDs.
However, several of them are not in ISO 3166-1.

 2·16 days ago
2·16 days agoOr you could just… learn to use the modern internet that 60% of internet traffic uses? Not everyone has a dedicated IPv4 anymore, we are in the days of mobile networks and CGNAT. IPv4 exhaustion is here today.
Where are you getting 60%? Google’s IPv6 Adoption page has it under 50% still:
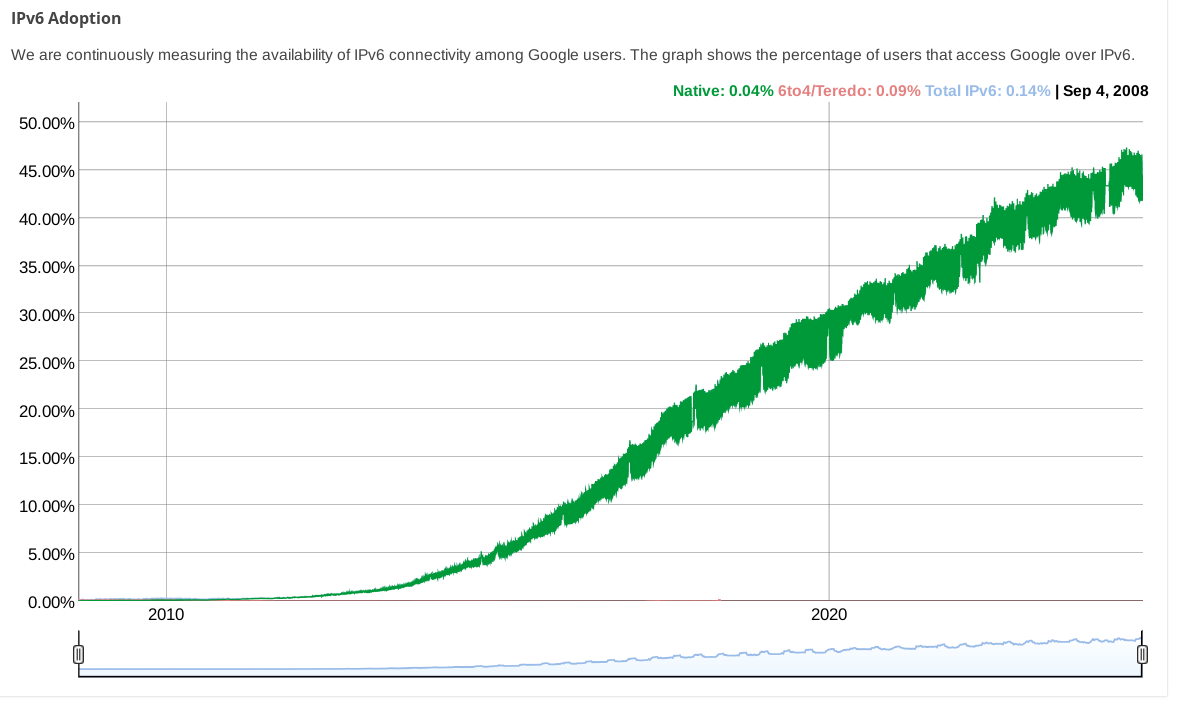
(while other stats pages from big CDNs show even less)

 1·16 days ago
1·16 days agoIf you have
::/0in your AllowedIPs and v6 connections are bypassing your VPN, that is strange.What does
ip route get 2a00:1450:400f:801::200e(an IPv6 address for google) say?I haven’t used wireguard with NetworkManager, but using
wg-quickit certainly adds a default v6 route when you have::/0inAllowedIPs.

 2·16 days ago
2·16 days agoYou could edit your configuration to change the wireguard connection’s
AllowedIPsfrom0.0.0.0/0to0.0.0.0/0,::/0so that IPv6 traffic is routed over it. Regardless of if your wireguard endpoint actually supports it, this will at least stop IPv6 traffic from leaking.

 3·16 days ago
3·16 days agoipv4 with an extra octet
that was proposed as “IPv4.1” on April 1, 2011: https://web.archive.org/web/20110404094446/http://packetlife.net/blog/2011/apr/1/alternative-ipv6-works/

 4·25 days ago
4·25 days agoyep, the concept of a “personal carbon footprint” was literally invented by an advertising agency working for British Petroleum https://www.theguardian.com/commentisfree/2021/aug/23/big-oil-coined-carbon-footprints-to-blame-us-for-their-greed-keep-them-on-the-hook

 291·1 month ago
291·1 month agoThis video is full of jarring edits which initially made me wonder if someone had cut out words or phrases to create an abbreviated version. But, then I realized there are way too many of them to have been done manually. I checked the full original video and from the few edits i manually checked it seems like it is just inconsequential pauses etc that were removed: for instance, when Linus says “the other side of that picture” in the original there is an extra “p” sound which is removed here.
Yet another irritating and unnecessary application of neural networks, I guess.

 7·1 month ago
7·1 month agoLemmy added an alt text field for image-only posts a few versions ago; it would be nice if more people would use it.
At least this post does link to the mastodon post which it is a screenshot of.

 20·1 month ago
20·1 month agoI really don’t get how its different than a search engine
Neither did this guy.
The difference is that LLM output is (in the formal sense) bullshit.

 11·2 months ago
11·2 months agoThe tone which comes across in the video (linked from the other post I linked to in this post’s description) is unfortunately much less amicable than this article conveys.

 61·2 months ago
61·2 months agothe guy speaking off camera in the linked 3min 30s of the video is Ted Ts’o, according to this report about the session.

 2·5 months ago
2·5 months agoE: old thinkpad gang input: take the time to reapply thermal grease to the cpu at some point. It makes a huge difference.
What’s a “gang input”?
😂 it’s an input to this discussion from a member of the group of people (“gang”) who have experience with old thinkpads. and yes, if your old thinkpad (or other laptop) is overheating and crashing, reapplying the thermal paste is a good next step after cleaning the fans.

 5·6 months ago
5·6 months agoxzbot from Anthony Weems enables to patch the corrupted liblzma to change the private key used to compare it to the signed ssh certificate, so adding this to your instructions might enable me to demonstrate sshing into the VM :)
Fun :)
Btw, instead of installing individual vulnerable debs as those kali instructions I linked to earlier suggest, you could also point debootstrap at the snapshot service so that you get a complete system with everything as it would’ve been in late March and then run that in a VM… or in a container. You can find various instructions for creating containers and VMs using debootstrap (eg, this one which tells you how to run a container with
systemd-nspawn; but you could also do it with podman or docker or lxc). When the instructions tell you to rundebootstrap, you just want to specify a snapshot URL likehttps://snapshot.debian.org/archive/debian/20240325T212344Z/in place of the usual Debian repository url (typicallyhttps://deb.debian.org/debian/).

 27·6 months ago
27·6 months agoA daily ISO of Debian
testingor Ubuntu 24.04 (noble) beta from prior to the first week of April would be easiest, but those aren’t archived anywhere that I know of. It didn’t make it in to any stable releases of any Debian-based distros.But even when you have a vulnerable system running sshd in a vulnerable configuration, you can’t fully demo the backdoor because it requires the attacker to authenticate with their private key (which has not been revealed).
But, if you just want to run it and observe the sshd slowness that caused the backdoor to be discovered, here are instructions for installing the vulnerable liblzma deb from snapshot.debian.org.

 1·6 months ago
1·6 months agoYou can use Wireshark to see the packets and their IP addresses.
https://www.wireshark.org/download.html
https://www.wireshark.org/docs/
A word of warning though: finding out about all the network traffic that modern software sends can be deleterious to mental health 😬

 2·6 months ago
2·6 months agoI do have wireguard on my server as well, I guess it’s similar to what tailscale does?
Tailscale uses wireguard but adds a coordination server to manage peers and facilitate NAT traversal (directly when possible, and via a intermediary server when it isn’t).
If your NAT gateway isn’t rewriting source port numbers it is sometimes possible to make wireguard punch through NAT on its own if both peers configure endpoints for eachother and turn on keepalives.
Do you know if Yggdrasil does something similar and if we exchange data directly when playing over Yggdrasil virtual IPv6 network?
From this FAQ it sounds like yggdrasil does not attempt to do any kind of NAT traversal so two hosts can only be peers if at least one of them has an open port. I don’t know much about yggdrasil but from this FAQ answer it sounds like it runs over TCP (so using TCP applications means two layers of TCP) which is not going to be conducive to a good gaming experience.
Samy Kamkar’s amazing pwnat tool might be of interest to you.

 2·6 months ago
2·6 months agoI have a device without public IP, AFAIK behind NAT, and a server. If I use bore to open a port through my server and host a game, and my friends connect to me via IP, will we have big ping (as in, do packets travel to the server first, then to me) or low ping (as in, do packets travel straight to me)?
No, you will have “big ping”. bore (and everything on that page i linked) is strictly for tunneling which means all packets are going through the tunnel server.
Instead of tunneling, you can try various forms of hole punching for NAT traversal which, depending on the NAT implementation, will work sometimes to have a direct connection between users. You can use something like tailscale (and if you want to run your own server, headscale) which will try its best to punch a hole for a p2p connection and will only fall back to relaying through a server if absolutely necessary.

 5·6 months ago
5·6 months agoSee https://github.com/anderspitman/awesome-tunneling for a list of many similar things. A few of them automatically setup letsencrypt certs for unique subdomains so you can have end-to-end HTTPS.





The headline should mention that they’re breaking 22-bit RSA, but then it would get a lot less clicks.
A different group of Chinese researchers set what I think is the current record when they factored a 48-bit number with a quantum computer two years ago: https://arxiv.org/abs/2212.12372
I guess the news here is that now they’ve reached 22 bits using the quantum annealing technique which works on D-Wave’s commercially-available quantum computers? That approach was previously able to factor an 18-bit number in 2018.
🥂 to the researchers, but 👎 to the clickbait headline writers. This is still nowhere near being a CRQC (cryptanalytically-relevant quantum computer).